Integrate AWS IAM Identity Center (successor to AWS Single Sign-On) with AWS Lake Formation fine-grained access controls - Global Intelligence and Insight Platform: IT Innovation, ETF Investment

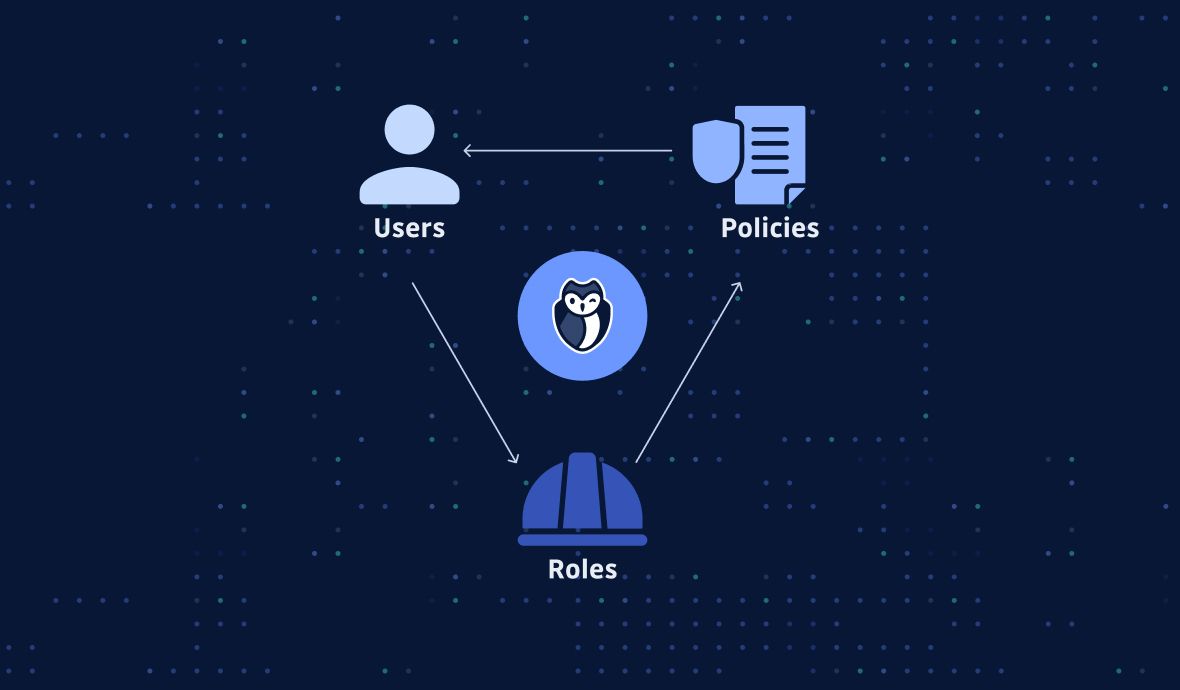
Integrate AWS IAM Identity Center (successor to AWS Single Sign-On) with AWS Lake Formation fine-grained access controls | AWS Big Data Blog

Should Data Centers Have Common Infrastructure Security Standards? | Data Center Knowledge | News and analysis for the data center industry
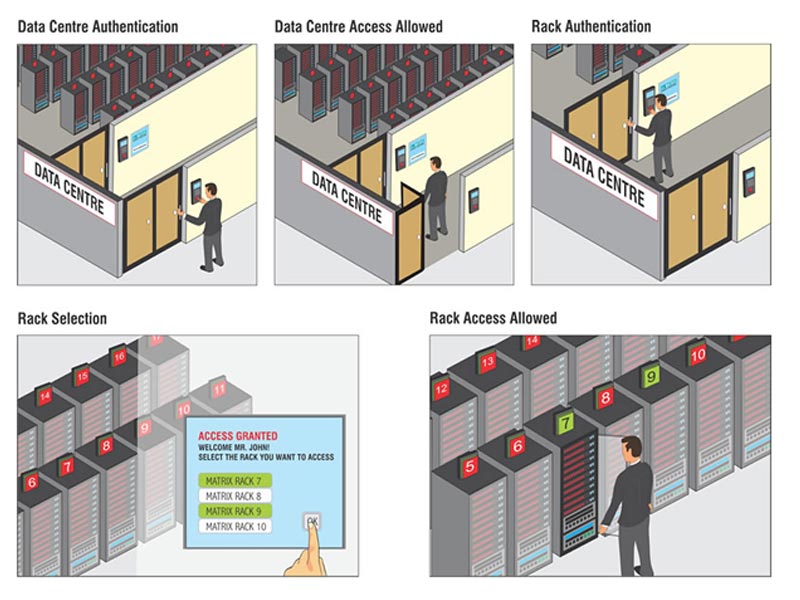
Matrix access control data centre solution | INDUSTRIAL SAFETY REVIEW | Fire Industry Magazine | Safety Magazine India | Security Magazine India | Life Safety Magazine | Occupational Health Safety Magazine

Integrate AWS IAM Identity Center (successor to AWS Single Sign-On) with AWS Lake Formation fine-grained access controls - Global Intelligence and Insight Platform: IT Innovation, ETF Investment

Integrate AWS IAM Identity Center (successor to AWS Single Sign-On) with AWS Lake Formation fine-grained access controls - Global Intelligence and Insight Platform: IT Innovation, ETF Investment